Depending on the sites employees visit on their mobile devices malware can be downloaded onto mobile devices that aren t protected by antivirus software or a mobile security app.
Mobile device security threats risks and actions to take.
Discussing the increasing security threats to mobile devices something we haven t talked about before on the podcast series and some ways to combat these.
In 2014 kaspersky detected almost 3 5 million pieces of malware on more than 1 million user devices.
Trend micro mobile security has advanced protection capabilities that can identify known threats and prevent them from damaging mobile devices or compromising data.
The point is to get across the fact that you expect employees to take mobile security seriously and that threats can come from almost anywhere.
Every enterprise should have its eye on these eight issues.
Or not properly protected from a variety of security threats.
1 everything from your operating system to your social network apps are potential gateways.
Here are some practical steps that will help you minimize the exposure of your mobile device to digital threats.
Mobile security threats may sound scary but here are six steps you can take to help protect yourself from them.
Keep your software updated.
Only 20 percent of android devices are running the newest version and only 2 3 percent are on the latest release.
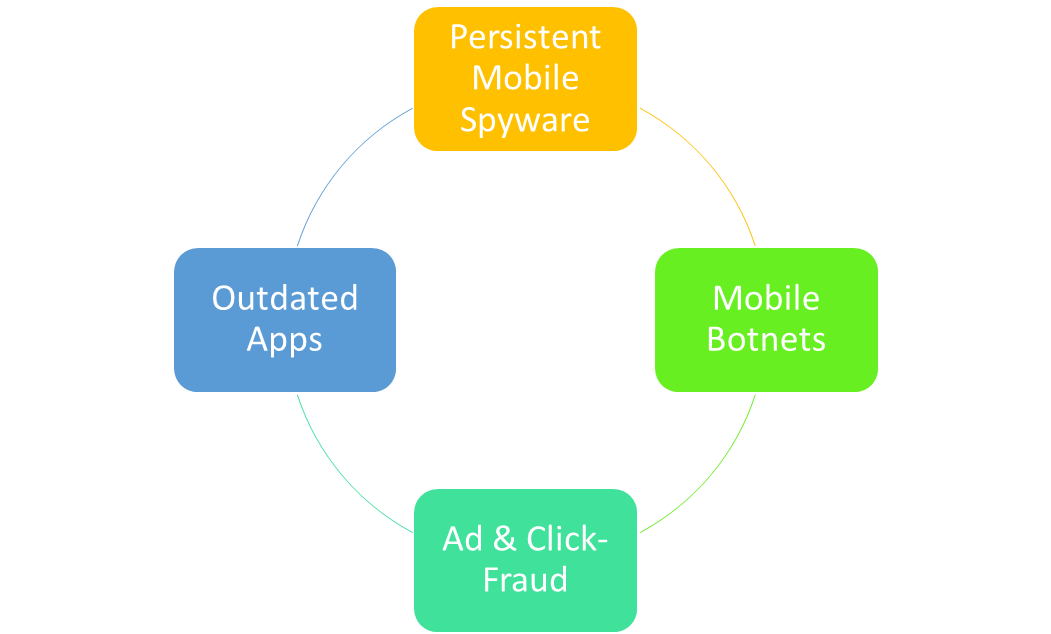
Some of the security threats include malware specifically designed for mobile devices i e.
Vulnerability when employees are using mobile devices.
Mobile threat detection can spot security threats to mobile devices or vulnerabilities based on system changes and metrics by monitoring oses apis and network traffic.
8 mobile security threats you should take seriously in 2020 mobile malware.
But not all is lost.
Cso and network world covering a variety of security and risk issues.
Some mobile security threats are more pressing.
Mobile threat detection unified endpoint management uem and microvirtualization take system defense further.
Mobile threat researchers identify five new threats to mobile device security that can impact the business.
Mobile device security threats risks and actions to takemobile device security threats risks and actions to take transcripttranscript.
6 biggest business security risks and how you can fight back.
Users could also take advantage of multilayered mobile security solutions that can protect devices against online threats malicious applications and even data loss.